5 Fatal Mistakes for the Security of Any Business
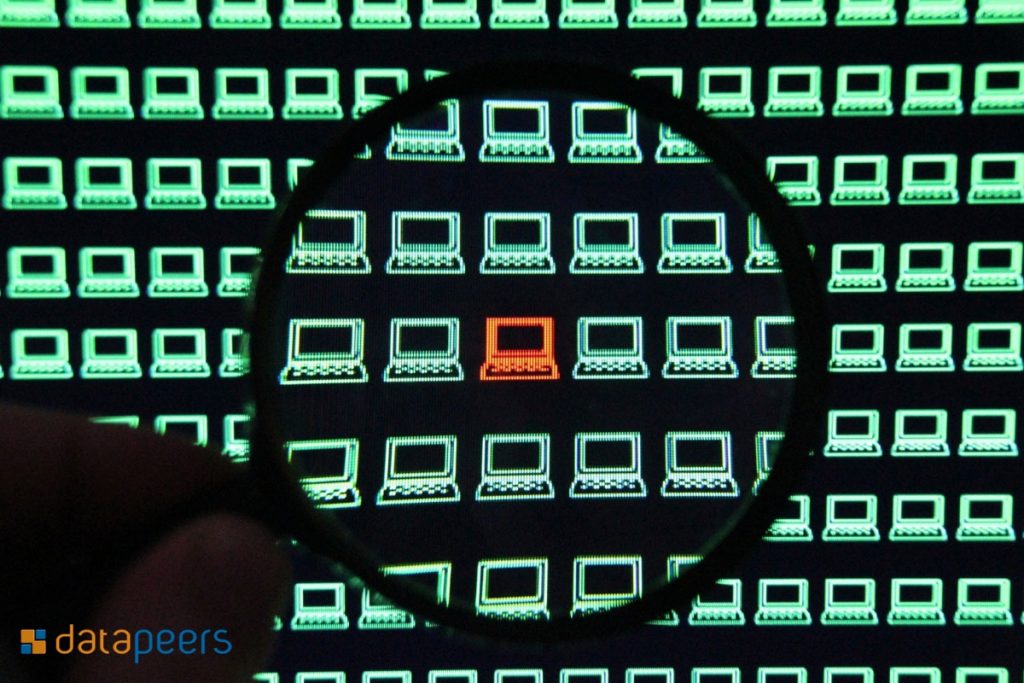
Information security in companies is an increasingly debated topic. Companies need to protect themselves to ensure their data is not lost in the event of a computer attack or natural disaster. Although there is growing concern about this topic, many companies still make mistakes that can totally compromise business continuity. In today’s article we present the 5 fatal errors for the security of any business!
Document control: the pillars of security
Documents contain valuable information about companies, so close security control is very important. Lost information can seriously compromise the entire continuity of the business. In today’s article, we cover the main pillars of security in document control!
Availability
It is essential that documents are available for consultation whenever needed. The information should be available and suitable for immediate use whenever needed. Therefore, it is essential that documents are stored in an easily accessible place (either in digital or physical format). Information access processes should be simple and practical, so as to make consultation as easy as possible. However, we must not forget that each employee should have access only to the documents they really need to work. If all employees have access to all documents, it is almost impossible to detect the source of any information leakage, for example.
Integrity
Documents should be kept intact for easy review. No documents should be scratched, stained or damaged that prevent them from being read correctly. In the case of digital documents, the files cannot be corrupted. In addition, documents must be protected in such a way that they are not unduly altered. There must be strict rules so that documents can only be changed by those authorized to do so.
Confidentiality
“The secret is the soul of business”: the phrase is old, but it still makes sense. In today’s business world, where cyber threats are around the corner, it is essential to protect your business data, to ensure that your competition doesn’t figure out what you are planning and also to protect your confidential data. its customers and other stakeholders. All companies are aware of the need to protect data. Tools like Datapeers help companies mask their data. Masking sensitive data is an essential component of a data security plan. Datapeers reduces the risk of data breach by replacing sensitive data with fictional but realistic data. Masked data maintains referential integrity and is statistically defined, enabling testing, analysis, and business processes. The primary use of masked data is in nonproduction environments, including test and development environments.
Extra tip:
As much as the IT manager does his or her best, problems can always exist as computer threats are increasingly sophisticated. A disaster recovery plan can be the salvation of a company. This document contemplates all actions and procedures to be taken in case of failures, in order to recover the computer services without compromising the data. Problems with servers, machine failures and viruses on the network are some of the problems that can happen in a company and compromise all security. RAAS is a service managed 24 hours a day and 7 days a week to ensure availability of your applications.
Find how to protect against key data security threats
Recently, a study found that most hotels don’t adequately protect the data that collects. Increasingly, we are faced with news of this type, which is worrying given the increased security threats. In addition to the increase in these threats, companies still face the “heavy hand” of the GDPR: in Portugal, the new legislation has already made its first “victims” through penalties for offenders. In a digital age where we deal with information every day, we must know how to protect ourselves from the main threats to data security. We’ve prepared 5 key tips to make sure your information is not lost or exposed!
How to modernize your business without compromising security?
Digital transformation is one of the themes of business moments. All the organizations intend to adopt systems that allow them to modernize their processes and a consequent improvement of the results. However, one of the issues that most worries managers in this area is the possible lack of security that a business modernization can bring. However, it is possible to modernize your business without compromising security. Let’s know how in this article!
Key features to increase the security of your business
Businesses live in a digital age and all the information we need to work on a daily basis is stored in a virtual environment. Thus, it is very important to ensure that the most important data in an organization remains protected from potential threats. A security breach can compromise the survival of a business, so it is imperative that companies leverage the most important tools to protect data. In today’s article, we’ve covered key features to increase the security of your business!
Information Security Policy
The security policy is a document developed by the company that records the principles of security that the company adopts and that must be followed by the employees. The security policy should be applied to all information systems, both desktop and mobile. For the policy to be respected, it is essential that top managers participate in its implementation and that there are clarification sessions on each point in this document. Sanctions should also be created for non-compliant employees, as this will make it easier to ensure that employees comply with all standards.
Data masking
Data masking aims at creating a structurally identical version of the data, but not the same as the original version. This technique creates a database with fictitious but realistic information that can be used for testing and training purposes. Data masking solutions offer a variety of sophisticated scrambling techniques to protect sensitive data, irreversibly replacing them with data that is not real, while maintaining the referential integrity of the database. It is increasingly important that companies adopt this technique as computer attacks are becoming more sophisticated, which makes them more unpredictable and more lethal. Datapeers offers a variety of sophisticated scrambling techniques to protect sensitive data, replacing them irreversibly with fictitious but realistic data.
Disaster Recovery Plan
A disaster recovery solution is a very complete process that guarantees data protection and recovery in the event of a failure. Backup is part of disaster recovery, but it is only one of its components. Disaster recovery is a very complete solution since in addition to copying the data it also ensures its restoration efficiently in case of natural disasters or infrastructure failures. This type of solution has as its main objective to eliminate (or at least to minimize on a large scale) the downtime of a company due to failures. RAAS is a disaster recovery service totally managed by specialized equipment and gives you the possibility to recover a virtual server in seconds.
Use updated antivirus on all devices
Incredibly, there are still companies that don’t look at antivirus as an important tool and completely underestimate its use. It is essential to use a good antivirus and ensure that it is always up to date, because only this way you can avoid the entry of viruses. The free antivirus we find on the Web is not able to protect the organization in all its layers, so you should always opt for a full premium version.
Have a good backup policy
It is essential that the most important information of your company has several copies, so that there is no risk of losing data forever. If you saved the data on external disks or pen drives a few years ago, it is now completely advisable to use the Cloud because it is one of the most reliable and reliable solutions on the market. In addition to having your data stored in a secure location, you can access it from anywhere and from any device, as long as you have access to the Internet.
Overview of 2018: everything that has changed throughout the year in the security industry
The end of the year is approaching and it is time to make a review about everything that happened this year. The business security industry has brought a lot of buzz this year and it’s important to look at what has changed over the last few months so we can be prepared to receive 2019! In today’s article, we cover everything that has changed throughout the year in the security industry.
Read More
Find how to safeguard private data on mobile devices
The trend is global: people are increasingly using mobile devices for everything. Nowadays, Internet access is mostly done through these devices and its evolution makes it possible to access the world wide web from anywhere in the World. People no longer go to the Internet; they live permanently online. On a personal level, there are no doubts about the changes and advantages that the mobile devices have brought, and at the corporate level the advantages are already evident: ability to work from any location, possibility to send e-mails by mobile phone, possibility to attend meetings, among many others. But not everything is good in the mobile world. Storing data on devices of this type raises security issues that if not thought out and handled in a timely manner can jeopardize the overall security of the enterprise. In today’s article, we leave you some tips for safeguarding private data on mobile devices!
Tips for managing and analyzing a large volume of data
The key for an effective decision making is the ability to extract the most important insights from the data the company has. However, because of the high number of data that is generated every day, it is not always easy to get the best out of the information. Managers are constantly looking for new ways of managing data, so that they can keep abreast of what is going on in the business and so they can consciously decide. In today’s article, we leave you important tips for managing and analyzing a large volume of data!
The 7 Deadly Sins of Corporate Security
Data security is very important for business success as more and more consumers and other stakeholders are concerned about the privacy of the information they provide to businesses. Ensuring the confidentiality of business data is a daily struggle in companies and employees need to be aware of the importance of information security. There are still many security holes that lead to data loss and consequent monetary losses. Let’s talk about the 7 Deadly Sins of Corporate Security!
Internet of Things and the main security challenges
The Internet of Things (IoT) has the power to change the way we live and the way we work. Nowadays, the cost of accessing the Internet is very low compared to the beginning of the technology age. Mobile devices are becoming more adept and more devices are built with network connectivity and built-in wi-fi. All these conditions create the ideal scenario for the Internet of Things and for its action in the business world. In a very simplified way, Internet of Things aims to connect any device to the Internet. According to Gartner, by the year 2020 there will be more than 26 billion devices connected to the network. At home, this concept aims to make life easier for people, but its application will also have an impact on the business world. In a world so connected and everything is connected to everything, the security challenges are immense. In this article we will analyze the main security challenges that the Internet of Things brings us! Read More